Table of Contents
WordPress is the most popular CMS available in the market today. Experts attribute the undisputed market share of 42% owned by WordPress to its flexibility that makes it suitable for both enterprise businesses as well as SMBs.
However, just like anything else, WordPress’s flexibility makes it highly vulnerable to cybersecurity attacks. That is unless you actively take measures to protect your site from these threats.
If you think that your WordPress site is secure, then think twice. Stats show that over 90,000 hacking attacks are made in a minute on WordPress sites. Imagine waking up to such a cybersecurity attack on your business website one fine morning!
If you’re going through this guide, then kudos to you. You’re on the right track towards seeking measures to protect your enterprise site from hacker attacks.
But, we have to warn you beforehand—there is no such thing as a “perfectly secure website.” According to WordPress, “security is risk reduction, not risk elimination.”
And that is what we’re going to explore in this exhaustive guide to enterprise WordPress security.
So, let’s dive deep and explore the different aspects of WordPress security for Enterprise websites—starting with why you need WordPress security, how to secure WordPress out of the box, the most common security threats, and 21 top WordPress security best practices.
Why Do You Need WordPress Security?
When we talk about WordPress security, the first question that may arise in your mind is—why you need WordPress security. In this section, let’s address this question and talk about why enterprises need to take active steps to ensure WordPress security.
1. Save Your Business’ Reputation
For growing businesses, open-ended security threats are like ticking bombs—ready to blow up your business’ reputation any time. Cybersecurity attacks on enterprises make for big news. This is because the customers’ information and privacy are at stake.
Cybersecurity attacks on your WordPress website may scar your business’ reputation for a long time. You may lose a large chunk of your existing client base and lose new business opportunities as well.
All this will damage your company’s reputation, lead to bad PR, and stunt your business’ growth by a good few years. Thus, investing in WordPress website security can save your business from a bad reputation.
2. Prevent Loss of Revenue
The hacking of your WordPress website can cause some serious monetary losses as well.
Hackers are always looking for backdoors and vulnerabilities to hack your website and steal information. And if they succeed, they’ll probably steal your information, install malware, and distribute malware to your customers.
Hackers may restrict your access to your own website and demand ransom to help you regain access.
Moreover, you may also end up paying massive amounts of penalties and compensations to your customers—leading to a dip in your profits. You can prevent all of this by taking steps to curb any cybersecurity threats on your WordPress site.
3. Avoid Loss of SEO Rankings
Search engines such as Google have a reputation for prioritizing user experience more than anything else. So, it makes sense for search engines to rank only those websites that work on their website security.
In Google’s own words, “security is a top priority for Google.” This makes it evident that without security, your website will have a hard time gaining search engine visibility.
The converse is also true. When your website becomes a victim of hacker attacks, expect a drop in SEO rankings and visibility. Therefore, it is best to save your website from such unwelcome SEO surprises by focusing on WordPress site security.
4. Offer Better User Experience
At the end of the day, the kind of user experience you offer has a major impact on your business’s revenue growth and success. And website security has a direct impact on user experience. How?
By leaving threats and vulnerabilities open on your site, you’re putting your customers’ privacy and information at risk. When customers share contact information, payment details, and other sensitive information with your website, they place immense trust in your brand.
By working on your WordPress site’s security, you are essentially reassuring your customers and offering a better user experience.
Is WordPress Secure?
Is WordPress really as secure as you’d want it to be? Have you made the wrong choice of CMS? All these questions may be currently wandering your mind. There is no short answer to this question, so let’s take a look.
There is no doubt in the fact that WordPress websites are popular targets for hackers.
In fact, Sucuri, a cybersecurity provider, did a study recently and found that 94% of all the CMS-powered websites that were hacked belonged to WordPress. And that there was a 4% growth in this number from 2018 to 2019.
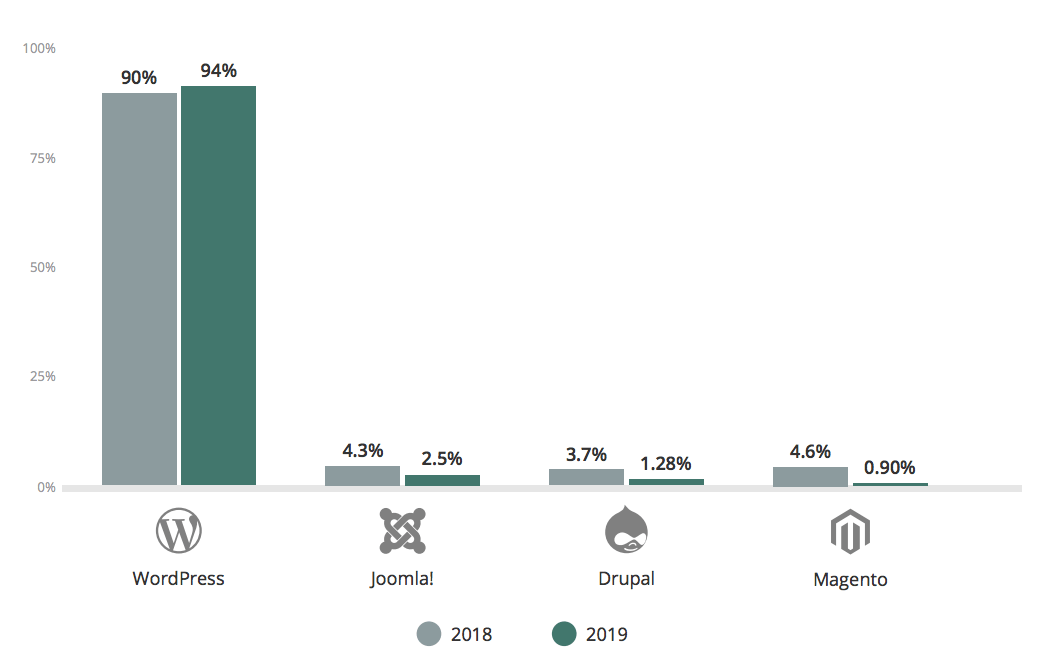
But, to give you more context, WordPress does power 42% of the web. So, it makes sense when we say that hackers love targeting WordPress sites. Hence, blaming WordPress solely for security breaches doesn’t seem fair.
WordPress, at its core, is quite secure as it is backed by a team of experts and engineers who are constantly identifying security threats and releasing security patches. In fact, from the time of its launch till today, more than 2,500 security vulnerabilities have been patched.
Now, WordPress is an open-source CMS, which means its code is open for anyone to work on, modify, and share. This is what makes the platforms flexible and attributes to their popularity.
However, WordPress’s open-source nature gives hackers access to its code and practice on it. Any hacker can insert a piece of malicious code into the WordPress core and make it vulnerable to cyber-attacks.
Ultimately, it is up to us, the end-users, to take measures to work on the risk reduction of our WordPress site.
We can sum this section up by saying that WordPress is secure, provided you take website security more seriously, educate yourself about the different security threats, and follow best practices to nip the problem in the bud.
7 Most Common WordPress Security Threats
As mentioned in the previous section, it is important that you take your WordPress site’s security more seriously. And, the first step towards it is to educate yourself about the most common WordPress security threats causing troubles for webmasters everywhere.
1. Brute-Force Attacks
Brute-force attacks are a common type of cybersecurity attack where hackers use trial-and-error to figure out your login info. Hackers usually run automated scripts to gain access to your site.
Once the hackers gain access to your website, there are many ways in which they can exploit it. They can steal sensitive information, spread malware and cause disruptions, place spam ads on your site, ruin your website’s reputation, and many more.
Using strong passwords, limiting login attempts, and implementing two-factor authentication are some of the common ways of preventing brute-force attacks.
2. Cross-Site Scripting (XSS)
Beware of cross-site scripting or XSS vulnerabilities as these are the most common vulnerabilities found in WordPress plugins. Cross-site scripting is when a hacker introduces a malicious piece of code in your website’s backend.
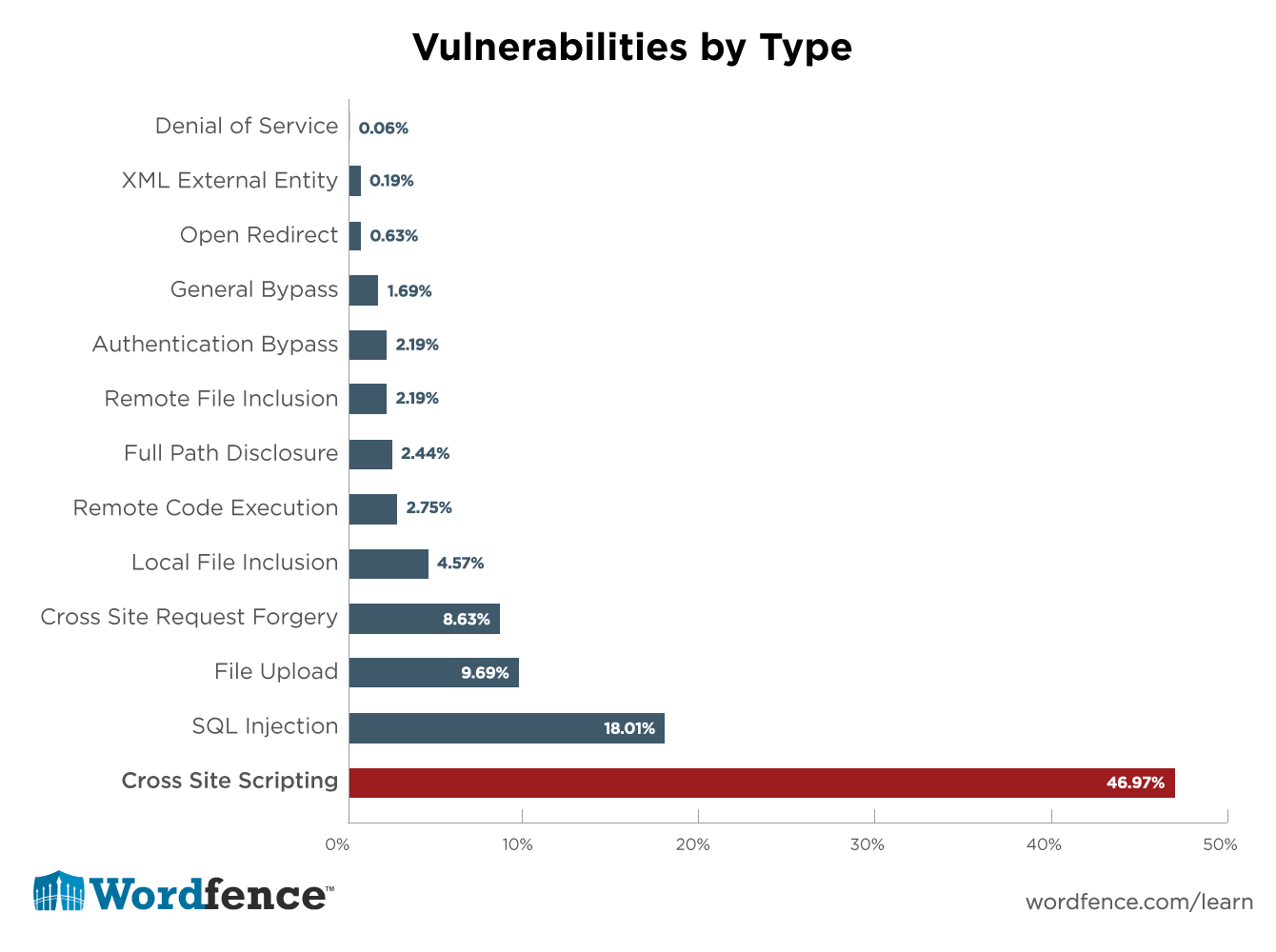
The end-user is unaware of these malicious scripts and thus may fall prey to suspicious activities by these hackers. Hackers can obtain cookie or session data this way. You can refer to WordPress’ security recommendations to understand how you can avoid such cross-site scripting attacks.
3. Database Injections
In the case of a database injection or SQL injection, hackers find a way to place a malicious piece of code in your database.
This is similar to a cross-site scripting attack but happens in a database. Hackers inject this harmful SQL code through some kind of user input available on your website.
Once injected, hackers can gain unauthorized access to personal data and payment information. Attackers can even gain access to your backend servers and perform a denial-of-service (DoS) attack as a consequence.
4. Backdoors
A backdoor attack is a process where hackers use malware to surpass your website’s authentication measures and security requirements. In simple terms, hackers use backdoors to gain unauthorized access to your website by bypassing the standard WordPress login.
The worst part about backdoor attacks is that these may be hidden and go unnoticed for a long period of time.
Once hackers gain access through backdoors, they may lurk around your site anytime. They can use it to access sensitive information and perform other malicious activities.
Hackers usually implement such backdoor attacks with the help of phishing emails encouraging software downloads. Clicking on such links opens up a backdoor for the hackers to gain access to your site.
5. Denial-of-Service (DoS) Attacks
A denial of service attack is when your website and the entire network are shut down, thus preventing authorized users from gaining access to your site.
Hackers perform such attacks by overloading your website with excessive information or flooding it with high traffic that leads to a crash.
Hackers target high-profile organizations such as government organizations, banks, etc., with DoS attacks.
Another type of DoS attack is the Distributed Denial of Service or DDoS attack, where multiple entities attack a single target from different locations. The effects of DDoS attacks are worse than DoS attacks.
6. Phishing
Phishing is one of the simplest ways for hackers to carry out cyberattacks on WordPress admins. Attackers usually do this by posing as a legitimate company and sending an email to WordPress admins containing malware links.
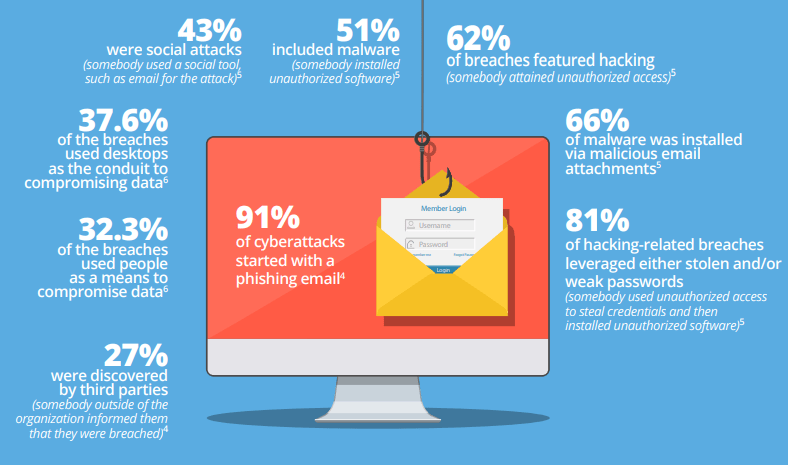
By clicking on such links, hackers can access your personal information, WordPress user credentials, and so on. Phishing attacks are quite common. In fact, surveys show that around 91% of cyber attacks start with a phishing email.
But the good news is that educating yourself and your employees about phishing activities is a sufficient measure to avoid such attacks.
7. Hotlinking
Hotlinking is when attackers embed your website’s content on another website with a direct file URL without your permission. This is a type of stealing where it appears as though the content is their own.
Through hotlinking, the other website is able to steal your bandwidth and consume your hosting resources. So it may seriously impact your site’s performance.
WordPress sites usually fall prey to hotlinking attacks through common vulnerabilities through which hackers gain easy access. These vulnerabilities can be due to your WordPress themes, plugins, or outdated WordPress versions.
WordPress Security Best Practices
By now, you would have a better idea about the most common types of WordPress security threats that you must be aware of.
As mentioned before, WordPress does pose some security threats because of its open-source and flexible nature. However, it is up to you to take measures to protect your website and data against such threats.
In this section, let’s have a look at some best practices that you must follow to ensure the maximum security of your WordPress website.
1. Secure WordPress Hosting
WordPress hosting plays a key role in determining the server-level security of your website. Hence, it is important to tread with caution when you are picking your hosting provider.
Secure hosting providers take active measures to protect the servers from cyber attacks. These include keeping the software and hardware up-to-date, monitoring the network for suspicious activity, and preventing large-scale DDOS attacks.
The risk of an attack is higher in the case of a shared WordPress hosting plan, as hackers can gain access to your website from other sites through cross-site contamination. However, you can lower this risk by opting for a managed hosting service provider.
2. Use the Latest PHP Version
As you might already know, WordPress is written in PHP scripting language. Thus, PHP forms the backbone of your WordPress website. Any vulnerabilities left open here can help hackers gain access to your website’s backend.
It is important to note that PHP supports each release version for a span of 2 years. During this support period, security issues are fixed and patched very frequently, thus securing your site’s backend.
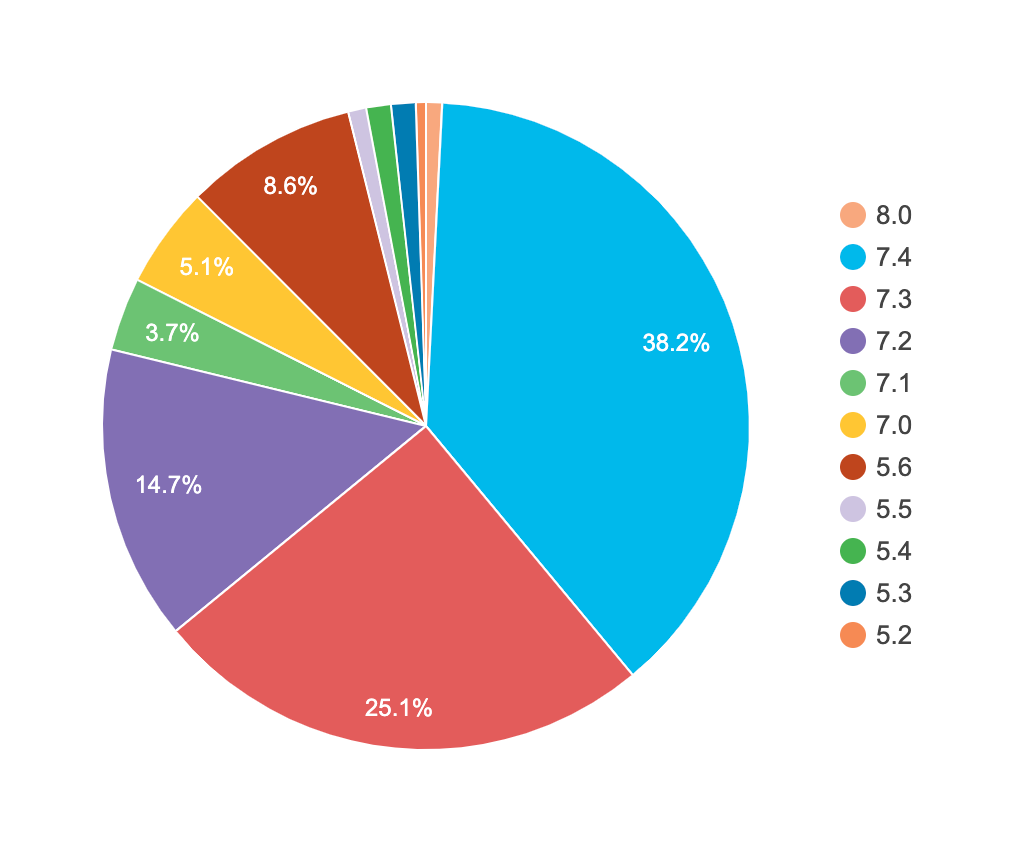
PHP’s latest version now is 8.0, and it offers support for versions 7.3 and 7.4. All the other versions are not offered support by PHP.
However, you’d be alarmed to know that 36.1% of WordPress sites are still using PHP versions below 7.3, thus making them vulnerable to cyber-attacks.

3. Have Strong Usernames and Passwords
Stealing passwords is one of the easiest ways for hackers to attack your site. And WordPress users make things easier for hackers by setting weak usernames and passwords.
Here are some best practices that you can follow to make sure the WordPress site is secured by strong user authentication:
- Use two-factor authentication for your WordPress login.
- Use strong passwords that are a combination of letters, numbers, and special characters.
- Do not store your WordPress login information on notes, documents, email, etc. Instead, try using password managers such as 1Password or LastPass.
- Install anti-virus software and enable your computer’s firewall.
4. Update to the Latest Versions
Outdated WordPress core, plugins, and themes are a common way through which hackers gain access to your website.
WordPress open-source CMS is constantly updated with bug fixes and security patches. It is crucial that you not miss these security enhancements and updates.
Therefore, make sure that you regularly check your WordPress dashboard for any new core updates or updates from themes and plugins. Update right away, and then make sure that everything continues to work as expected.
5. Secure WordPress Admin
WordPress admin that usually can be accessed with the URL domain.com/wp-admin is the doorway to many security threats and issues.
Hackers mainly target WordPress admins and find a way to fix a backdoor to your site’s backend. Hence, hardening WordPress admin security can be a powerful way to mitigate some imminent WordPress security threats.
Here is a list of measures you can take to secure WordPress admin:
- Changing the default /wp-admin URL to something less obvious can be a significant first step. Most hackers are aware of this URL, and it makes things easier for them.
- You can also try limiting login attempts with the help of WordPress plugins like Limit Login Attempts Reloaded. Such plugins enable you to set the number of login attempts and lockout period to keep you safe from scripts that try login info combinations.
- Other great ways to harden security is by automatically logging out idle users and limiting user permissions to a bare minimum of what is actually needed.
6. Two-Factor Authentication
As mentioned before, two-factor authentication is a great way to curb security threats from brute-force attacks. Two-factor authentication is when a WordPress authentication becomes a two-step process.
The users first have to enter their login credentials. Following this, a one-time password is usually sent to the user’s cell phone through text or email as a second-level authentication.
Two-factor authentication makes it almost impossible for hackers to run scripts and guess weak login information as they cannot gain access to the users’ cell phones. Consider setting up two-factor authentication for both—your WordPress (with a plugin) and hosting provider login.
7. Use a Firewall
A firewall is a type of network security device that monitors incoming and outgoing traffic from your network and blocks any unauthorized traffic.
In the case of a WordPress website, a firewall will act as an added security measure between the network that hosts your WordPress site and other external networks. A web application firewall will block any malicious activity from incoming to your website network.
To add a firewall, you can install a web application firewall plugin.
8. Have an HTTPS SSL Certificate
HTTPS is a protocol that allows the secure transfer of information between your WordPress site and the users’ browsers. You can do this by installing an SSL certificate.
Though SSL certificates are crucial for websites that involve financial transactions, today, the need for SSL is extended for every website. This has been stressed over time and repeatedly by search engines such as Google.
This is because an SSL certificate secures the transfer of sensitive information between your website and users. Apart from maintaining a secure connection, an SSL certificate also helps with SEO.
Moreover, SSL certificates are vital for building trust with your audience and offering a good user experience. In fact, browsers such as Chrome throw warnings to users saying that a website is “Not Secure”—not something that your users will overlook.
9. Harden wp-config.php
The wp-config.php file is the configuration file for WordPress installation, and it plays a major role in your site’s security. This is because this file stores vital information such as DB connection details and security keys that shouldn’t land in the hands of hackers at any cost.
The first step to harden the wp-config.php file is by moving it from its default location, which is the root directory, to a different location that is not that easily accessible.
Another measure you can take to harden wp-config.php is by changing file permissions on this file. WordPress recommends modifying file permissions—”This file is initially created with 644 permissions, and it’s a hazard to leave it like that.”
10. Disable XML-RPC
XML-RPC is a communication protocol that enables your WordPress site to connect external applications. WordPress introduced the XML-RPC protocol by default since the release of its 3.5 version.
The problem with this protocol is that it makes brute force attacks much easier for hackers as they can use the system.multicall function to try thousands of password combinations with much fewer requests.
This may even go undetected by your login limiter WordPress plugin and hence can be dangerous.
Most websites, including yours, may not be using the XML-RPC protocol. So, why leave this unnecessary vulnerability open? You can check if your website is using this protocol by using a free WordPress XML-RPC validator.
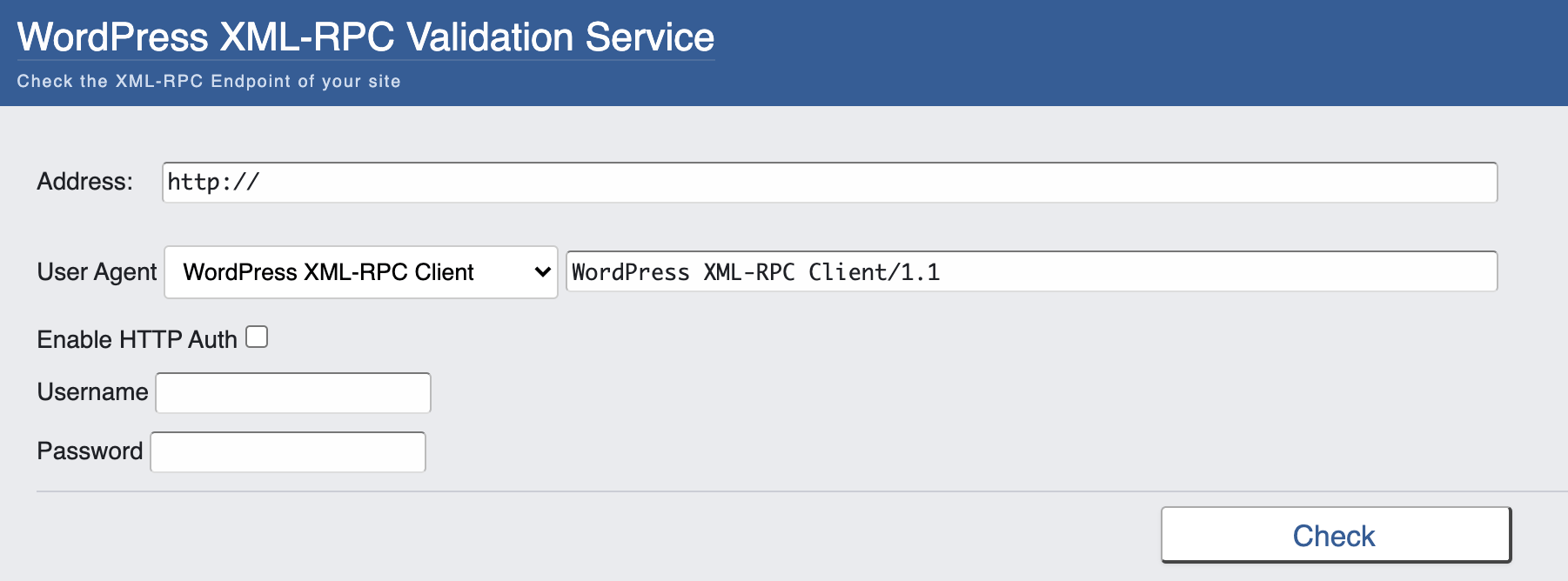
If you are not using it, then you can easily disable the XML-RPC protocol for your WordPress website using plugins such as Disable XML-RPC-API plugin.
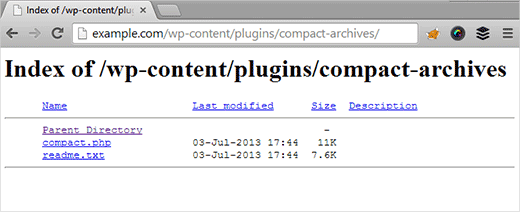
11. Disable Directory Indexing and Browsing
Directory browsing is a process where hackers browse through your WordPress directory and find vulnerabilities.
They can browse through your files and look for any vulnerabilities that they can use to penetrate your WordPress site’s backend. Through directory browsing, hackers can also retrieve other details such as personal data, images, and more.
To avoid this from happening, it is crucial that you disable directory browsing and indexing for your WordPress website. You can refer to this detailed guide on disabling directory browsing and indexing in WordPress by WPBeginner.
12. Hide WordPress Version
As discussed before, it is better to keep your WordPress up-to-date with the latest core version updates. However, if for some reason you have not updated your WordPress version, and even otherwise, consider hiding the version from public view.
This again goes back to the same underlying principle of security—the lesser information hackers have, the lesser threat they pose to your website.
Having this in mind, go ahead and hide your WordPress versions from the header of your site’s source code and in the default readme.html file.
13. HTTP Security Headers
HTTP security headers offer an added level of security for your WordPress website as these tell the browser about how to behave when handling your site’s content. There are different types of security headers that you can add, and each serves a different purpose.
For example, the Content-Security-Policy header defines content sources that are approved and thus prevents the browser from loading content from any unapproved sources.
This works great for preventing Cross-Site Scripting or XSS attacks that we had talked about in the section on most common WordPress security threats.
Here’s a list of the ix most important security headers that you should implement on your WordPress site:
- Content-Security-Policy
- X-XSS-Protection
- HTTP Strict Transport Security (HSTS)
- X-Frame-Options
- Expect-CT
- X-Content-Type-Options
- Feature-Polic
If you are looking for a detailed guide on checking current security headers on your WordPress site and how you can implement them, then you can refer to this article on security headers by KeyCDN.
14. Use a WordPress Security Plugin
Of course, how can we forget about WordPress security plugins that do a great job of hardening the security of your WordPress website? Here’s a list of top WordPress security plugins that you should consider installing:
- Sucuri
- Jetpack Security
- Wordfence Security
- WPScan
- BulletProof Security
- iThemes Security Pro
- SecuPress
- WP fail2ban
Typically, these plugins offer basic and advanced security features such as firewalls, two-factor authentication, IP blacklisting, limiting login attempts, updates of WordPress security keys, malware scanning, and similar more.
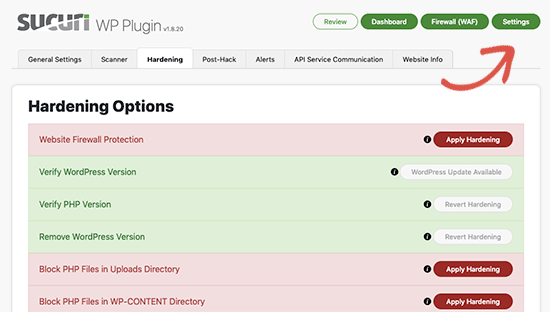
You can browse through each of these WordPress security plugins and pick the one (or more than one) that best suits your security needs.
15. Ensure Database Security
As mentioned before, your WordPress database also poses a security risk for hackers to exploit. Therefore, hardening the security of your database is equally important as everything else.
Here are a few steps you can take to ensure the security of your WordPress database:
- Change the default name of your WordPress database.
- Modify the default table prefixes.
- Change the default database login credentials to something stronger.
16. Secure Connections
Having secure connections is also a part of ensuring the security of your WordPress site. Here are some precautions you should take to ensure the same:
- Make sure that your hosting provider offers SFTP or SSH protocols for file transfers instead of the standard FTP protocols.
- Avoid logging into your WordPress site from public networks.
- Change your router’s default range to something unique.
- Ensure the highest possible level of encryption on your WiFi connection.
17. Conduct Regular WordPress Security Scans
Apart from enabling security measures for your WordPress site, it is also vital that you frequently monitor your site to make sure there are no vulnerabilities that you may have missed. Again, WordPress plugins come to your rescue.
There are a variety of WordPress plugins that offer security scans on a regular basis, such as:
- Wordfence Security
- iThemes Security
- Sucuri
- Jetpack Security
- Defender
- Bulletproof Security
- All In One WP Security and Firewall
- Security Ninja
- Titan
While a periodic manual review of your site’s security is always good, it may take a considerable amount of time and needs expertise. Such WordPress security scan plugins make things a lot easier and leave less room for missed security threats.
18. File and Directory Permissions
Unauthorized access to your files and directories can be another way for hackers to gain entry into your WordPress website. Therefore, you must take steps to ensure that only required file and server permissions are offered to users.
For example, if a user doesn’t have access or the need to write in a file or execute it, then you should only offer read permission to the user, and not write and execute. The same applies to directory browsing permissions as well.
19. Prevent Hotlinking
As discussed in the section on most common security threats, hotlinking is when attackers embed your website’s content on another website with a direct file URL without your permission. Hotlinking allows hackers to steal your bandwidth and consume your hosting resources.
You can prevent hotlinking with the help of most of the WordPress security plugins mentioned before. If you are serving images through a Content Delivery Network (CDN), then you can get hotlink protection from your CDN provider.
20. Take Frequent WordPress Backups
As we’ve stressed several times in this article, there is no way you can make your website 100% secure. You can only reduce threats but not completely eliminate them.
Therefore, you need a fallback mechanism in case things go wrong despite all the security measures that you’ve taken.
The fallback mechanism that we are referring to is taking frequent backups of your WordPress site. Taking frequent manual or automated backups of your website will help you stay assured that you can bring your website back to life in case of a cyberattack.
For automated backups, you can check with your hosting provider. Or, you can install WordPress plugins such as CodeGuard, VaultPress, or BlogVault that offer frequent automated WordPress website backups.
21. DDoS Protection
We’ve touched upon DoS and DDoS attacks in the previous section on common WordPress security threats. In case of such attacks, your entire WordPress network is shut down, preventing authorized users from gaining access to your website.
You can protect your WordPress website from DoS and DDoS attacks by using monitoring tools like Cloudflare to analyze traffic patterns and looking for any anomalies. Or, you can invest in third-party security services that offer DoS and DDoS protection as a part of their security plan.
Wrapping Up
To conclude, we can say that the security of your WordPress website lies entirely in your hands. At its core, WordPress is secure. However, the added flexibility features make it more vulnerable to security attacks, just like in the case of any other widely used open-source software.
In this educational guide, we’ve discussed the different types of WordPress security threats that you should be aware of and the best practices that will allow you to steer clear of almost all of them.
Remember that educating yourself about WordPress security is the first step to mitigating risks and preventing attacks, which you’ll gain from this comprehensive guide. And if you need a WordPress expert to ensure complete cybersecurity for your business website, you’re in the right place.
References
- WordPress
- WordPress Security Statistics
- WordPress’ security recommendations
- Phish Protection
- LastPass
- WordPress – Login Attempts Reloaded
- WordPress Plugin – Web Application Firewall
- WordPress Plugin – 2FA
- WordPress – HTTPS SSL Certificate
- Kinsta
- WordPress – Changing File Permission
- WordPress XML-RPC validator
- WordPress Plugin – Disable XML-RPC-API
- WPBeginner
- KeyCDN
Your Enterprise WordPress Development Partner!
Schedule a free consultation call to discuss your enterprise WordPress requirements.
(or Contact Us)